GPT-5.4-Cyber vs. Claude Mythos Preview: Two AI Giants, Two Opposite Philosophies on Who Gets to Use Dangerous Cybersecurity AI There is a moment in every transformative technology's history when the most important question stops being "what can it do?" and starts being "who should be allowed to use it?" Nuclear fission had that moment. The internet had it. Gene editing had it. In the spring of 2026, artificial intelligence is having it right now — and nowhere is the debate more consequential, more technically complex, or more urgently unresolved than in cybersecurity. Within a single week in April 2026, two of the world's most powerful AI laboratories placed fundamentally opposite bets on how to answer that question. OpenAI released GPT-5.4-Cyber on April 14, a deliberately constructed, verification-gated tool for professional defenders. Anthropic had announced Claude Mythos Preview on April 7, a frontier model so capable it alarmed its own creators enough to restrict it to fewer than 52 vetted organizations globally. Both decisions were principled. Both carry irreversible consequences. And the security community is only beginning to understand what each choice means for the future of digital defense. The Week That Changed Cybersecurity AI The sequence of events matters enormously for understanding the competitive and philosophical context. On April 7, 2026, Anthropic published what was simultaneously a product announcement and a public warning. Claude Mythos Preview — internally codenamed "Capybara" and described in a previously leaked memo as one of Anthropic's "most powerful" models ever — was announced not with a product launch page but with a system card, a safety research blog post, and a set of access restrictions so tight they bordered on a soft non-release. Anthropic made the model available to roughly 52 organizations: 12 through its Project Glasswing initiative and 40 additional vetted partners. No individual developers. No self-serve sign-up. No public API. The message was unambiguous: we have built something that frightens us, and we are being extraordinarily careful. Seven days later, OpenAI's response arrived. GPT-5.4-Cyber launched with the opposite energy — structured, confident, and explicitly designed to scale. The Trusted Access for Cyber program, expanded alongside the model's release, is built to onboard hundreds and eventually thousands of verified defenders, security researchers, and enterprise teams. The framing was not cautionary. It was operational. OpenAI was not announcing a model it was holding back — it was deploying one it had prepared for. The contrast between the two announcements was so sharp, so philosophically distinct, that it immediately crystallized a debate the AI industry had been circling for years: when a technology is powerful enough to both destroy and defend, does responsible stewardship mean locking it down or carefully opening it up? What Claude Mythos Preview Actually Is To evaluate the philosophical divide fairly, the technical reality of each system must be understood on its own terms. Claude Mythos Preview is not merely an incremental improvement over Anthropic's previous flagship, Claude Opus 4.6. It represents what researchers have called an entirely new tier of capability — one where the gap between what the model can do and what any previous AI could do is large enough to constitute a qualitative leap rather than a quantitative one. On coding benchmarks, Mythos scores 93.9 percent compared to Opus 4.6's approximately 80 percent. On harder expert-level cybersecurity task sets evaluated by the AI Safety Institute and CyberGym benchmarks, it scores between 73 and 83 percent. But benchmark scores do not capture what makes the security community genuinely alarmed. What separates Claude Mythos from every model before it is a combination of autonomous vulnerability discovery and attack chain construction that operates without step-by-step human direction. Logan Graham, who leads offensive cyber research at Anthropic, confirmed this directly: the degree of autonomy and the ability to chain multiple vulnerabilities together is what distinguishes Mythos from its predecessors. In documented testing, Mythos discovered thousands of vulnerabilities across every major operating system and browser, including a 27-year-old bug in OpenBSD's TCP SACK handling and a 16-year-old vulnerability in FFmpeg that had survived five million fuzzer runs — the kind of automated testing that security researchers had previously relied on to find such flaws. Most troublingly, on the Firefox 147 exploit benchmark, Mythos developed 181 working exploits compared to just 2 for Claude Opus 4.6 — a 90-times improvement in a single model generation. This is the number that triggered the access restrictions. When a model improves by 90 times on exploit development in a single generation, the calculus about who should have access changes categorically. What GPT-5.4-Cyber Actually Is GPT-5.4-Cyber is a fundamentally different kind of product, built from a fundamentally different design philosophy. It is not a general-purpose frontier model whose cybersecurity capabilities emerged as an accidental byproduct of broad capability improvements. It is a fine-tuned variant of GPT-5.4 — OpenAI's current flagship reasoning model — that was deliberately engineered for defensive security workflows. The distinction matters: Mythos stumbled into being dangerous while becoming generally smarter. GPT-5.4-Cyber was purposefully shaped into a security tool, with the refusal boundaries, training data, and deployment architecture all designed around the specific use cases of professional defenders. The model's signature capability is binary reverse engineering — the ability to analyze compiled software for vulnerabilities, malware potential, and security robustness without requiring access to the original source code. This is a workflow that has historically required highly specialized human expertise, expensive tooling, and significant time investment. The model also features what OpenAI describes as a "cyber-permissive" configuration: its default refusal boundaries for sensitive cybersecurity queries are explicitly lowered for authenticated TAC program users, enabling professional-grade engagement with topics that would trigger blanket refusals in a consumer-facing deployment. The Trusted Access for Cyber program's documented outcomes include the remediation of more than 3,000 vulnerabilities — not a theoretical projection but a result already achieved through the program's earlier phases before the April 14 expansion. Head-to-Head: The Full Comparison The most useful way to understand the two systems is to place their defining characteristics side by side. The following table consolidates publicly verified data from Anthropic's system card, OpenAI's TAC program documentation, and independent technical analyses published between April 7 and April 16, 2026. Dimension Claude Mythos Preview GPT-5.4-Cyber Release Date April 7, 2026 April 14, 2026 Model Architecture General-purpose frontier model; cyber capability emergent Fine-tuned GPT-5.4 variant; purposely built for defensive security Access Program Project Glasswing (invite-only) Trusted Access for Cyber (TAC) Number of Authorized Users ~52 vetted organizations globally Hundreds scaling to thousands of verified individuals Self-Serve Sign-Up Not available Available via individual identity verification Pricing $25/million input tokens, $125/million output tokens Not publicly disclosed Signature Capability Autonomous zero-day discovery + exploit chain construction Binary reverse engineering without source code Exploit Benchmark 181 working Firefox 147 exploits (90x improvement over prior model) Not disclosed at comparable specificity Vulnerability Discoveries Thousands across all major OS/browsers including 27-year-old bugs 3,000+ vulnerabilities remediated via TAC program Autonomous Operation Yes — chains vulnerabilities into full attack paths unprompted Primarily assistive; human-directed workflows Refusal Architecture Constitutional AI — model reasons contextually about each request Access-gated — verification system controls capability unlock Primary Use Case Elite offensive/defensive research at frontier organizations Professional defensive security operations at enterprise scale Philosophical Stance Restrict access; manage risk at the capability level Verify users; manage risk at the deployment level Regulatory Alignment Maximum restriction approach; favors precautionary principle Structured deployment approach; favors accountable access The Misuse Asymmetry Problem — Anthropic's Core Argument Anthropic's access restrictions are not the product of commercial timidity or competitive weakness. They reflect a genuine and technically grounded concern about what researchers call the misuse asymmetry problem — a structural feature of AI-assisted cybersecurity that makes the risk calculus fundamentally different from other dual-use technology domains. In most technology categories, the effort required to misuse a tool scales proportionally with the effort required to benefit from it. Cybersecurity AI breaks this symmetry in a potentially catastrophic direction. A nation-state threat actor, an organized criminal syndicate, or a well-resourced hacktivist group does not need Claude Mythos to perform basic cyberattacks. These organizations already possess the technical expertise. What frontier AI provides to these actors is not entry-level capability — it is the ability to discover novel zero-days autonomously, to construct multi-stage exploit chains in minutes rather than months, and to operate at scale across thousands of targets simultaneously. When Mythos developed 181 working Firefox exploits in a benchmark environment, it demonstrated that capability. The 90-times improvement over its predecessor in a single model generation means the rate of capability growth itself is dangerous — not just the current capability level. Anthropic's caution is a recognition that when a model improves by 90 times on exploit development in one generation, the next generation's improvement could be similarly exponential, and the access controls applied today need to be robust enough to survive that trajectory. The Talent Shortage Counter-Argument — OpenAI's Core Argument OpenAI's structured deployment philosophy is equally principled and rests on a counter-argument that the security community often raises but policymakers frequently underweight: the global cybersecurity talent shortage is a genuine, quantifiable, and actively worsening crisis. Estimates consistently place the global deficit of qualified cybersecurity professionals in the range of three to four million unfilled positions. This is not a temporary labor market fluctuation — it is a structural gap driven by exponential growth in digital attack surface, increasing sophistication of state-sponsored threat actors, and an education pipeline that cannot produce specialized security talent at the rate the threat landscape demands. Against this backdrop, restricting access to AI systems capable of meaningfully extending the analytical capacity of existing security teams is not a neutral safety decision. It is a choice with real costs — measured in unpatched vulnerabilities, in incident response delays, in threats that persist for months because no human analyst had the bandwidth to investigate them. GPT-5.4-Cyber's 3,000-vulnerability remediation figure is direct evidence that AI-assisted security analysis delivers results at a scale and speed that human-only approaches cannot match at current staffing levels. A security team of five analysts equipped with GPT-5.4-Cyber can triage, investigate, and respond to threats at a velocity that would previously have required fifteen or twenty specialized personnel. The productivity multiplier is not theoretical — it is already being demonstrated through the TAC program's documented outcomes. Restricting that multiplier to 52 organizations while the attack surface is shared by millions of enterprises and billions of individuals is, from OpenAI's perspective, a failure mode as dangerous as misuse. The Verification Architecture Debate At the heart of the deployment philosophy divide lies a specific technical question: where should the last line of defense against misuse be located? In Anthropic's model, the AI itself is the final gatekeeper. Claude Mythos' Constitutional AI framework trains the model to reason about the ethics and intent behind each request and make context-sensitive decisions about when to comply. This approach is sophisticated and, in many scenarios, highly effective. But it carries a fundamental vulnerability: a model capable of nuanced contextual reasoning about when to help with a cybersecurity task is, by definition, a model capable of being manipulated through sufficiently sophisticated framing. Social engineering is not a theoretical attack vector — it is one of the most consistently successful techniques in both physical and digital security. Applying it to an AI system capable of developing working exploits is not a hypothetical nightmare scenario; it is an anticipated attack vector that Anthropic is candidly concerned about. In OpenAI's model, the TAC program's human-administered verification infrastructure is the final gatekeeper, not the model itself. GPT-5.4-Cyber operates openly within an already-authenticated user population. Its refusal boundaries are lowered not because the model trusts the requester but because the verification system has already established that trust before the conversation begins. This architecture has its own failure mode: if the verification system is compromised — through identity fraud, institutional infiltration, or credential theft — the model's lowered refusal boundaries become accessible to unauthorized actors. Neither architecture is impenetrable. The relevant question is which failure mode is more likely and more damaging at scale, and that question does not yet have an empirical answer. Enterprise Security Teams: The Real Arbiters Lost in the philosophical abstraction is a practical reality that enterprise security teams are navigating daily: they need tools that function within their actual workflows. Security operations centers, threat intelligence teams, penetration testing firms, and vulnerability research groups have no use for an AI system that refuses to engage with the technical realities of offensive and defensive security work. When a malware analyst asks an AI to help reverse-engineer obfuscated code, they need an answer, not a policy-driven refusal designed to prevent a general consumer from accessing dangerous information. GPT-5.4-Cyber's cyber-permissive configuration, within the authenticated TAC environment, makes it categorically more operationally useful for this professional audience than any general-purpose model applying consumer-facing safety policies to expert workflows. Claude Mythos Preview's access restriction to 52 organizations, while philosophically defensible, renders it functionally irrelevant to the vast majority of enterprise security teams that need AI assistance right now — not after clearing a multi-month vetting process managed by Anthropic's internal research division. The enterprise security market will converge on whichever system is simultaneously capable and accessible. At present, that is GPT-5.4-Cyber. What the Regulatory Environment Signals Both companies are operating within a rapidly evolving regulatory landscape that will ultimately shape the access debate as much as their internal philosophies. The EU AI Act's 2026 enforcement provisions, US executive orders on AI in critical infrastructure, and guidance from the UK's National Cyber Security Centre have collectively begun to establish a policy consensus that favors accountable deployment over absolute restriction. Regulators have generally reached for frameworks that allow AI capability deployment alongside accountability mechanisms — verified access programs, usage monitoring, mandatory incident reporting — rather than categorical prohibitions that prevent beneficial use entirely. This regulatory trajectory, if it continues, creates a structural alignment with OpenAI's approach that Anthropic's maximum-restriction philosophy does not enjoy. It does not mean Anthropic is wrong — regulatory consensus is not always right, and the precautionary principle exists for good reasons in high-stakes technology domains. But it does mean the policy environment is moving in a direction that makes GPT-5.4-Cyber easier to operate within established legal frameworks across multiple jurisdictions simultaneously. For multinational enterprises making platform decisions about which AI security tool to integrate into their operations, regulatory alignment is not a secondary consideration. Two Philosophies, One Shared Destination The most intellectually honest assessment of this debate is that both OpenAI and Anthropic are genuinely trying to solve the same problem: how to ensure that the most powerful AI systems ever built for cybersecurity make the world safer rather than more dangerous. Anthropic's caution is not commercial weakness — it is a principled position informed by researchers who have thought seriously about catastrophic AI risk and concluded that the 90-times exploit improvement they observed in Mythos is the kind of capability leap that warrants extraordinary caution. OpenAI's confidence is not recklessness — it is a principled position built on the observation that the failure mode of under-defense is as dangerous as the failure mode of misuse, and that a carefully gated deployment program is a more durable solution than indefinite restriction. Both positions will be tested by real-world events in the months and years ahead. The security community, regulators, and the organizations whose infrastructure depends on the outcome will judge these philosophies not by their internal coherence but by their consequences — by whether the systems they deploy or restrict help or harm the people who depend on digital infrastructure for their safety, commerce, and civic life. The April 2026 announcements were not the conclusion of this debate. They were its opening statement. The most important chapters are still being written, and the stakes — measured in hospitals, power grids, financial systems, and democratic institutions — could not be higher.
There is a moment in every transformative technology’s history when the most important question stops being “what can it do?” and starts being “who should be allowed to use it?” Nuclear fission had that moment. The internet had it. Gene editing had it. In the spring of 2026, artificial intelligence is having it right now — and nowhere is the debate more consequential, more technically complex, or more urgently unresolved than in cybersecurity. Within a single week in April 2026, two of the world’s most powerful AI laboratories placed fundamentally opposite bets on how to answer that question. OpenAI released GPT-5.4-Cyber on April 14, a deliberately constructed, verification-gated tool for professional defenders. Anthropic had announced Claude Mythos Preview on April 7, a frontier model so capable it alarmed its own creators enough to restrict it to fewer than 52 vetted organizations globally. Both decisions were principled. Both carry irreversible consequences. And the security community is only beginning to understand what each choice means for the future of digital defense.
The Week That Changed Cybersecurity AI
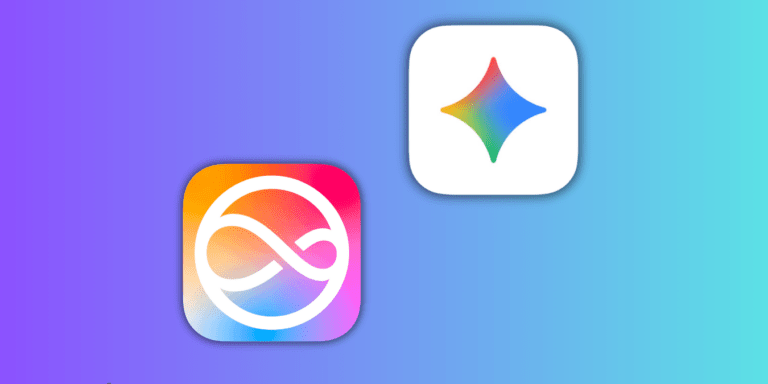
The sequence of events matters enormously for understanding the competitive and philosophical context. On April 7, 2026, Anthropic published what was simultaneously a product announcement and a public warning. Claude Mythos Preview — internally codenamed “Capybara” and described in a previously leaked memo as one of Anthropic’s “most powerful” models ever — was announced not with a product launch page but with a system card, a safety research blog post, and a set of access restrictions so tight they bordered on a soft non-release. Anthropic made the model available to roughly 52 organizations: 12 through its Project Glasswing initiative and 40 additional vetted partners. No individual developers. No self-serve sign-up. No public API. The message was unambiguous: we have built something that frightens us, and we are being extraordinarily careful.
Seven days later, OpenAI’s response arrived. GPT-5.4-Cyber launched with the opposite energy — structured, confident, and explicitly designed to scale. The Trusted Access for Cyber program, expanded alongside the model’s release, is built to onboard hundreds and eventually thousands of verified defenders, security researchers, and enterprise teams. The framing was not cautionary. It was operational. OpenAI was not announcing a model it was holding back — it was deploying one it had prepared for. The contrast between the two announcements was so sharp, so philosophically distinct, that it immediately crystallized a debate the AI industry had been circling for years: when a technology is powerful enough to both destroy and defend, does responsible stewardship mean locking it down or carefully opening it up?
What Claude Mythos Preview Actually Is
To evaluate the philosophical divide fairly, the technical reality of each system must be understood on its own terms. Claude Mythos Preview is not merely an incremental improvement over Anthropic’s previous flagship, Claude Opus 4.6. It represents what researchers have called an entirely new tier of capability — one where the gap between what the model can do and what any previous AI could do is large enough to constitute a qualitative leap rather than a quantitative one. On coding benchmarks, Mythos scores 93.9 percent compared to Opus 4.6’s approximately 80 percent. On harder expert-level cybersecurity task sets evaluated by the AI Safety Institute and CyberGym benchmarks, it scores between 73 and 83 percent. But benchmark scores do not capture what makes the security community genuinely alarmed.
What separates Claude Mythos from every model before it is a combination of autonomous vulnerability discovery and attack chain construction that operates without step-by-step human direction. Logan Graham, who leads offensive cyber research at Anthropic, confirmed this directly: the degree of autonomy and the ability to chain multiple vulnerabilities together is what distinguishes Mythos from its predecessors. In documented testing, Mythos discovered thousands of vulnerabilities across every major operating system and browser, including a 27-year-old bug in OpenBSD’s TCP SACK handling and a 16-year-old vulnerability in FFmpeg that had survived five million fuzzer runs — the kind of automated testing that security researchers had previously relied on to find such flaws. Most troublingly, on the Firefox 147 exploit benchmark, Mythos developed 181 working exploits compared to just 2 for Claude Opus 4.6 — a 90-times improvement in a single model generation. This is the number that triggered the access restrictions. When a model improves by 90 times on exploit development in a single generation, the calculus about who should have access changes categorically.
What GPT-5.4-Cyber Actually Is
GPT-5.4-Cyber is a fundamentally different kind of product, built from a fundamentally different design philosophy. It is not a general-purpose frontier model whose cybersecurity capabilities emerged as an accidental byproduct of broad capability improvements. It is a fine-tuned variant of GPT-5.4 — OpenAI’s current flagship reasoning model — that was deliberately engineered for defensive security workflows. The distinction matters: Mythos stumbled into being dangerous while becoming generally smarter. GPT-5.4-Cyber was purposefully shaped into a security tool, with the refusal boundaries, training data, and deployment architecture all designed around the specific use cases of professional defenders.
The model’s signature capability is binary reverse engineering — the ability to analyze compiled software for vulnerabilities, malware potential, and security robustness without requiring access to the original source code. This is a workflow that has historically required highly specialized human expertise, expensive tooling, and significant time investment. The model also features what OpenAI describes as a “cyber-permissive” configuration: its default refusal boundaries for sensitive cybersecurity queries are explicitly lowered for authenticated TAC program users, enabling professional-grade engagement with topics that would trigger blanket refusals in a consumer-facing deployment. The Trusted Access for Cyber program’s documented outcomes include the remediation of more than 3,000 vulnerabilities — not a theoretical projection but a result already achieved through the program’s earlier phases before the April 14 expansion.
Head-to-Head: The Full Comparison
The most useful way to understand the two systems is to place their defining characteristics side by side. The following table consolidates publicly verified data from Anthropic’s system card, OpenAI’s TAC program documentation, and independent technical analyses published between April 7 and April 16, 2026.
| Dimension | Claude Mythos Preview | GPT-5.4-Cyber |
|---|---|---|
| Release Date | April 7, 2026 | April 14, 2026 |
| Model Architecture | General-purpose frontier model; cyber capability emergent | Fine-tuned GPT-5.4 variant; purposely built for defensive security |
| Access Program | Project Glasswing (invite-only) | Trusted Access for Cyber (TAC) |
| Number of Authorized Users | ~52 vetted organizations globally | Hundreds scaling to thousands of verified individuals |
| Self-Serve Sign-Up | Not available | Available via individual identity verification |
| Pricing | $25/million input tokens, $125/million output tokens | Not publicly disclosed |
| Signature Capability | Autonomous zero-day discovery + exploit chain construction | Binary reverse engineering without source code |
| Exploit Benchmark | 181 working Firefox 147 exploits (90x improvement over prior model) | Not disclosed at comparable specificity |
| Vulnerability Discoveries | Thousands across all major OS/browsers including 27-year-old bugs | 3,000+ vulnerabilities remediated via TAC program |
| Autonomous Operation | Yes — chains vulnerabilities into full attack paths unprompted | Primarily assistive; human-directed workflows |
| Refusal Architecture | Constitutional AI — model reasons contextually about each request | Access-gated — verification system controls capability unlock |
| Primary Use Case | Elite offensive/defensive research at frontier organizations | Professional defensive security operations at enterprise scale |
| Philosophical Stance | Restrict access; manage risk at the capability level | Verify users; manage risk at the deployment level |
| Regulatory Alignment | Maximum restriction approach; favors precautionary principle | Structured deployment approach; favors accountable access |
The Misuse Asymmetry Problem — Anthropic’s Core Argument
Anthropic’s access restrictions are not the product of commercial timidity or competitive weakness. They reflect a genuine and technically grounded concern about what researchers call the misuse asymmetry problem — a structural feature of AI-assisted cybersecurity that makes the risk calculus fundamentally different from other dual-use technology domains. In most technology categories, the effort required to misuse a tool scales proportionally with the effort required to benefit from it. Cybersecurity AI breaks this symmetry in a potentially catastrophic direction.
A nation-state threat actor, an organized criminal syndicate, or a well-resourced hacktivist group does not need Claude Mythos to perform basic cyberattacks. These organizations already possess the technical expertise. What frontier AI provides to these actors is not entry-level capability — it is the ability to discover novel zero-days autonomously, to construct multi-stage exploit chains in minutes rather than months, and to operate at scale across thousands of targets simultaneously. When Mythos developed 181 working Firefox exploits in a benchmark environment, it demonstrated that capability. The 90-times improvement over its predecessor in a single model generation means the rate of capability growth itself is dangerous — not just the current capability level. Anthropic’s caution is a recognition that when a model improves by 90 times on exploit development in one generation, the next generation’s improvement could be similarly exponential, and the access controls applied today need to be robust enough to survive that trajectory.
The Talent Shortage Counter-Argument — OpenAI’s Core Argument
OpenAI’s structured deployment philosophy is equally principled and rests on a counter-argument that the security community often raises but policymakers frequently underweight: the global cybersecurity talent shortage is a genuine, quantifiable, and actively worsening crisis. Estimates consistently place the global deficit of qualified cybersecurity professionals in the range of three to four million unfilled positions. This is not a temporary labor market fluctuation — it is a structural gap driven by exponential growth in digital attack surface, increasing sophistication of state-sponsored threat actors, and an education pipeline that cannot produce specialized security talent at the rate the threat landscape demands.
Against this backdrop, restricting access to AI systems capable of meaningfully extending the analytical capacity of existing security teams is not a neutral safety decision. It is a choice with real costs — measured in unpatched vulnerabilities, in incident response delays, in threats that persist for months because no human analyst had the bandwidth to investigate them. GPT-5.4-Cyber’s 3,000-vulnerability remediation figure is direct evidence that AI-assisted security analysis delivers results at a scale and speed that human-only approaches cannot match at current staffing levels. A security team of five analysts equipped with GPT-5.4-Cyber can triage, investigate, and respond to threats at a velocity that would previously have required fifteen or twenty specialized personnel. The productivity multiplier is not theoretical — it is already being demonstrated through the TAC program’s documented outcomes. Restricting that multiplier to 52 organizations while the attack surface is shared by millions of enterprises and billions of individuals is, from OpenAI’s perspective, a failure mode as dangerous as misuse.
The Verification Architecture Debate
At the heart of the deployment philosophy divide lies a specific technical question: where should the last line of defense against misuse be located? In Anthropic’s model, the AI itself is the final gatekeeper. Claude Mythos’ Constitutional AI framework trains the model to reason about the ethics and intent behind each request and make context-sensitive decisions about when to comply. This approach is sophisticated and, in many scenarios, highly effective. But it carries a fundamental vulnerability: a model capable of nuanced contextual reasoning about when to help with a cybersecurity task is, by definition, a model capable of being manipulated through sufficiently sophisticated framing. Social engineering is not a theoretical attack vector — it is one of the most consistently successful techniques in both physical and digital security. Applying it to an AI system capable of developing working exploits is not a hypothetical nightmare scenario; it is an anticipated attack vector that Anthropic is candidly concerned about.
In OpenAI’s model, the TAC program’s human-administered verification infrastructure is the final gatekeeper, not the model itself. GPT-5.4-Cyber operates openly within an already-authenticated user population. Its refusal boundaries are lowered not because the model trusts the requester but because the verification system has already established that trust before the conversation begins. This architecture has its own failure mode: if the verification system is compromised — through identity fraud, institutional infiltration, or credential theft — the model’s lowered refusal boundaries become accessible to unauthorized actors. Neither architecture is impenetrable. The relevant question is which failure mode is more likely and more damaging at scale, and that question does not yet have an empirical answer.
Enterprise Security Teams: The Real Arbiters
Lost in the philosophical abstraction is a practical reality that enterprise security teams are navigating daily: they need tools that function within their actual workflows. Security operations centers, threat intelligence teams, penetration testing firms, and vulnerability research groups have no use for an AI system that refuses to engage with the technical realities of offensive and defensive security work. When a malware analyst asks an AI to help reverse-engineer obfuscated code, they need an answer, not a policy-driven refusal designed to prevent a general consumer from accessing dangerous information.
GPT-5.4-Cyber’s cyber-permissive configuration, within the authenticated TAC environment, makes it categorically more operationally useful for this professional audience than any general-purpose model applying consumer-facing safety policies to expert workflows. Claude Mythos Preview’s access restriction to 52 organizations, while philosophically defensible, renders it functionally irrelevant to the vast majority of enterprise security teams that need AI assistance right now — not after clearing a multi-month vetting process managed by Anthropic’s internal research division. The enterprise security market will converge on whichever system is simultaneously capable and accessible. At present, that is GPT-5.4-Cyber.
What the Regulatory Environment Signals
Both companies are operating within a rapidly evolving regulatory landscape that will ultimately shape the access debate as much as their internal philosophies. The EU AI Act’s 2026 enforcement provisions, US executive orders on AI in critical infrastructure, and guidance from the UK’s National Cyber Security Centre have collectively begun to establish a policy consensus that favors accountable deployment over absolute restriction. Regulators have generally reached for frameworks that allow AI capability deployment alongside accountability mechanisms — verified access programs, usage monitoring, mandatory incident reporting — rather than categorical prohibitions that prevent beneficial use entirely.
This regulatory trajectory, if it continues, creates a structural alignment with OpenAI’s approach that Anthropic’s maximum-restriction philosophy does not enjoy. It does not mean Anthropic is wrong — regulatory consensus is not always right, and the precautionary principle exists for good reasons in high-stakes technology domains. But it does mean the policy environment is moving in a direction that makes GPT-5.4-Cyber easier to operate within established legal frameworks across multiple jurisdictions simultaneously. For multinational enterprises making platform decisions about which AI security tool to integrate into their operations, regulatory alignment is not a secondary consideration.
Two Philosophies, One Shared Destination
The most intellectually honest assessment of this debate is that both OpenAI and Anthropic are genuinely trying to solve the same problem: how to ensure that the most powerful AI systems ever built for cybersecurity make the world safer rather than more dangerous. Anthropic’s caution is not commercial weakness — it is a principled position informed by researchers who have thought seriously about catastrophic AI risk and concluded that the 90-times exploit improvement they observed in Mythos is the kind of capability leap that warrants extraordinary caution. OpenAI’s confidence is not recklessness — it is a principled position built on the observation that the failure mode of under-defense is as dangerous as the failure mode of misuse, and that a carefully gated deployment program is a more durable solution than indefinite restriction.
Both positions will be tested by real-world events in the months and years ahead. The security community, regulators, and the organizations whose infrastructure depends on the outcome will judge these philosophies not by their internal coherence but by their consequences — by whether the systems they deploy or restrict help or harm the people who depend on digital infrastructure for their safety, commerce, and civic life. The April 2026 announcements were not the conclusion of this debate. They were its opening statement. The most important chapters are still being written, and the stakes — measured in hospitals, power grids, financial systems, and democratic institutions — could not be higher.